Feb 03, 2026
-
0 Comments
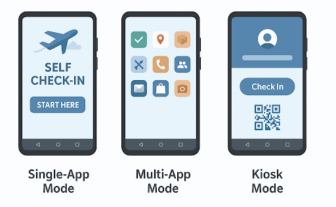
Why Locking down Your Devices to Single-App, Multi-App, and Kiosk Mode
Locking down Your Devices to Single-App, Multi-App, and Kiosk…
Feb 03, 2026
-
0 Comments
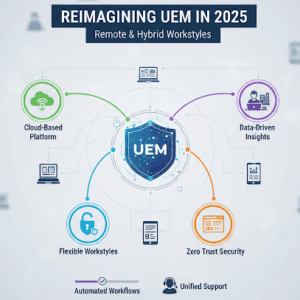
Support for Remote, Hybrid & Frontline Workers
Support for Remote, Hybrid & Frontline Workers: Redefining Endpoint…
Feb 03, 2026
-
0 Comments
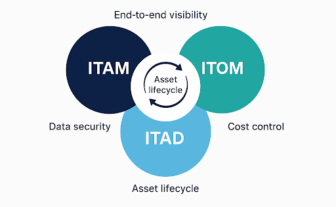
From Chaos to Control : How ITAM, ITOM and ITAD Align to Secure your enterprise
How ITAM, ITOM and ITAD Align to Secure your…

Feb 03, 2026
-
0 Comments
What Is Zero Trust and How Does It Impact Endpoint Security?
Never trust, always verify. That’s the principle behind Zero…

Dec 23, 2025
-
0 Comments
Integrating UEM with ITSM & CMDB: A Blueprint for Unified IT Operations
Blueprint for Unified IT Operations In today’s complex IT…
Dec 23, 2025
-
0 Comments
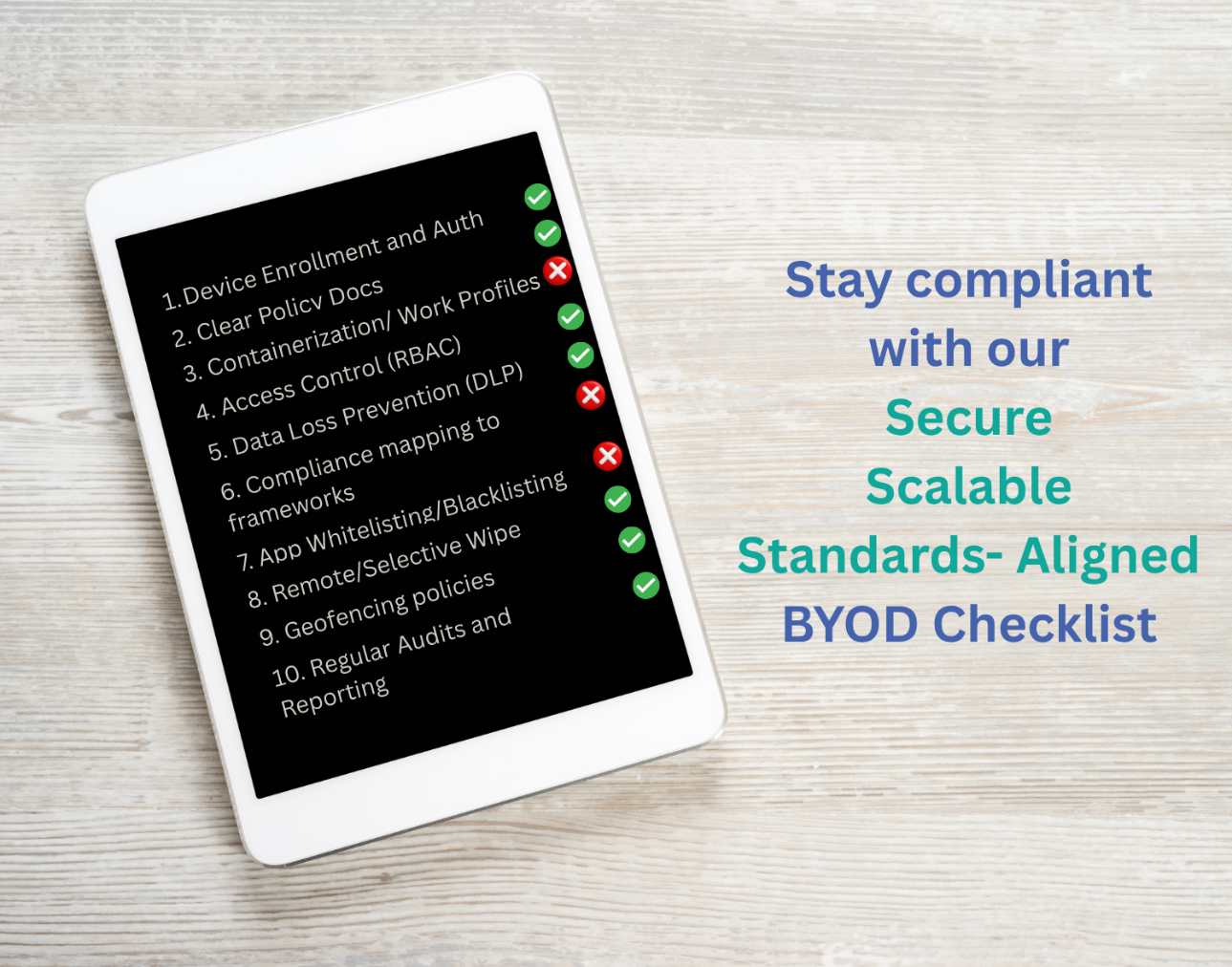
Is Your Organization Ready for BYOD? A 10-Point Compliance Checklist
Organization Ready for BYOD Compliance Checklist Bring Your Own…

Nov 20, 2025
-
0 Comments
Predictive Maintenance with Asset Intelligence: Stay One Step Ahead of Device Failures
Predictive Maintenance with Asset Intelligence: Stay One Step Ahead…

Nov 20, 2025
-
0 Comments
Shadow Apps vs. Sanctioned Apps: What Your Endpoint Data Is Telling You
What Are Shadow Apps and Why Do They Matter?…
Nov 20, 2025
-
0 Comments
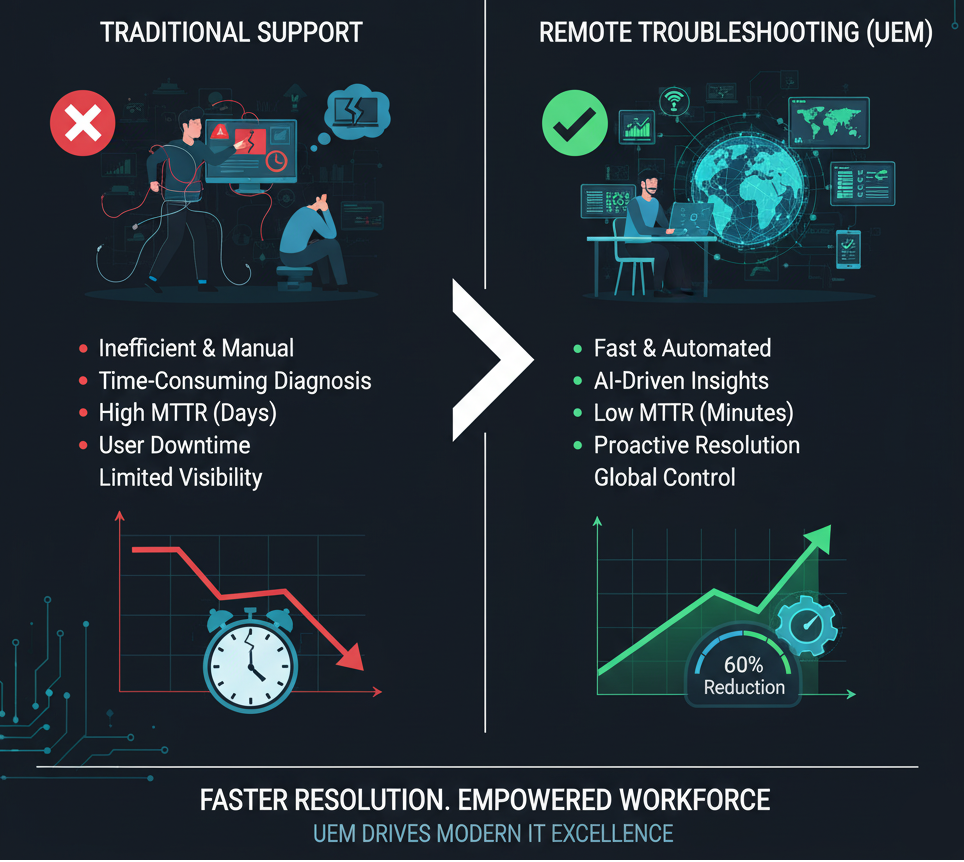
Remote Troubleshooting for the Win: Cut Down MTTR with UEM Insights
Remote Troubleshooting for the Win: Cut Down MTTR with…